M03 IPv4 Addresses, Subnetting and ARP
Internet Protocol version 4
Lecture Videos
Background
DARPA INTERNET PROGRAM PROTOCOL SPECIFICATION, 1. Motivation
The Internet Protocol is designed for use in interconnected systems of packet-switched computer communication networks. The internet protocol provides for transmitting blocks of data called datagrams from sources to destinations, where sources and destinations are hosts identified by fixed length addresses. The internet protocol also provides for fragmentation and reassembly of long datagrams, if necessary, for transmission through "small packet" networks.
Since its design in 1970 - 1980 the usage of Internet Protocol (IP) has exploded. The designers of IPv4 decided to use a 32 -bit field for addressing devices (with a theoretical maximum of 2^32 = 4 294 967 296 devices).
They never suspected that there (ever) would be a network that would have that many computers attached to it. And here we are today. Running out of IPv4 addresses. Because of that decision.
What exactly is IPv4 exhaustion?
"IPv4 exhaustion" doesn't mean that the Internet will stop working.
Instead, IPv4 exhaustion is the term used to describe when there will be no more unallocated IPv4 addresses available. But this will happen is several stages, and not necessarily in the order below:
- IANA exhausted its IPv4 free pool (3 February 2011)
- RIRs exhaust their unallocated pools
-
Expanding networks (ISPs, businesses, etc) exhaust their pools of unused addresses
-
Source: APNIC
The Internet Protocol occupies Layer 3 of the OSI Model.
The IPv4 currently amounts up to 70 - 80 percent of the world's Internet traffic, with the updated version IPv6 (Internet Protocol version 6) slowly, but surely taking over.
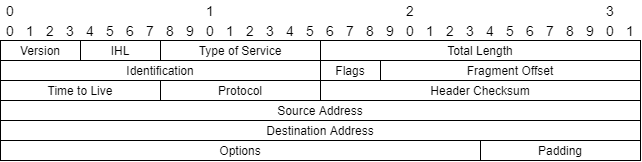
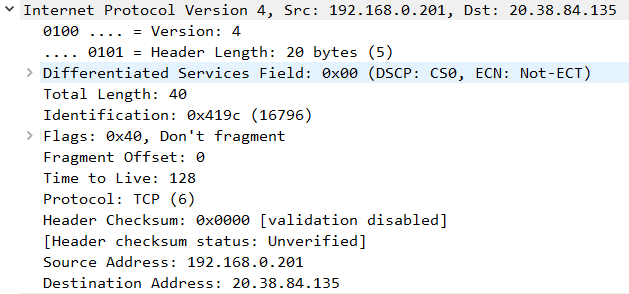
Internet Header Format
Every packet has a header. This is what an IPv4 packet header looks like.
Version
A field reserved to indicate version of the header. Either 4 or 6.
IHL - Internet Header Length
Points to the beginning of the data carried by the header. And so this field also indicates the end/length of the header.
Type of Service
The field is used to assure Quality of Service to packets whilst they travel through the data networks.
Total Length
What is the length of the datagram (including header & data).
Identification
A value set in the header to aid the receiver in reassembling.
Flags
Bits (true/false) that indicate can the packet be fragmented during transport. And if the received fragment is the last one.
Fragment Offset
Informs where in the whole datagram this current packet belongs to.
Time to Live
If this field is zero, this datagram cannot be forwarded. Once sent typically the value is 255 and is decreased by one per each routing decision.
Protocol
Indicates the next protocol carried by this packet. Be it TCP, UDP, ICMP or something else. IANA lists these protocols
Typical values on this course:
| Value | Protocol |
|---|---|
| 1 | ICMP |
| 6 | TCP |
| 17 | UDP |
Header Checksum
A verification field that the header in intact and hasn't suffered errors during transmit.
Source Address
The IPv4 address of the sender. Please see Addressing devices
Destination Address
The IPv4 address of the destination. Please see Addressing devices
Options
Options field can be present in datagrams. They have to be transmitted if present.
Padding
Padding is used to verify that the Header is divisionable by 32 bits.
Addressing devices
Lecture Video from this point forward
The 32 -bit address space
The address space is represented (to us, people) by four decimals with dots in between. The most classic example would be
192.168.0.1
Unfortunately computers do not process decimal numbers, but binaries so the same address in binary would be.
1100 0000 . 1010 1000 . 0000 0000 . 0000 0001
And the same in hexadecimal format.
C0.A8.00.01
Decimal format is the most common form. Hexadecimals can be seen in e.g. Wireshark captures, but rarely IP addresses are discussed with hexadecimals. Binary form is relevant in subnetting calculations.
Classful
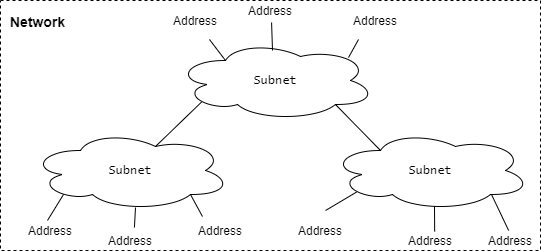
The idea that a Network is divided into subnetworks (or "subnets") is taken into account in addressing.
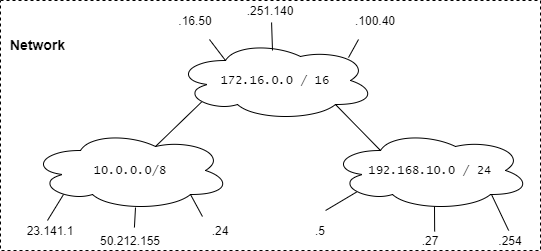
So we have a network that is divided into subnets that contain addresses. So the idea is as seen in the following figure
And to fill that idea with actual IP addresses brings us to:
Something new that is visible is the subnet mask represented by / 8, / 16 and / 24 in the drawing.
These are the basic subnet sizes of IPv4. The subnet mask declares: how many devices/addresses can fit into the subnet.
The Classful classes of IPv4 are:
| Class | Start of the binary sequence | Protocol | Addresses | Network Mask | Amount of devices |
|---|---|---|---|---|---|
| A | 0 |
8 bits of net, 24 bits of host | 0.0.0.0 - 127.255.255.255 | / 8 | 2^24 = 16 777 216 |
| B | 10 |
16 bits of net, 16 bits of host | 128.0.0.0 - 191.255.255.255 | / 16 | 2^16 = 65 536 |
| C | 110 |
24 bits of net, 8 bits of host | 192.0.0.0 - 223.255.255.255 | / 24 | 2^8 = 256 |
| D | 1110 |
- | 224.0.0.0 - 239.255.255.255 | - | Multicast |
| E | 110 |
- | 240.0.0.0 - 255.255.255.255 | - | Experimental |
Classless
Lecture Video from this point forward
As stated earlier, the IPv4 address space is exhausting. This called for an strategy to reserve addresses by allowing more dynamic use of subnet masks.
Further information can be read from the declaring RFC.
Classless Inter-domain Routing (CIDR): The Internet Address Assignment and Aggregation Plan
This memo discusses the strategy for address assignment of the existing 32-bit IPv4 address space with a view toward conserving the address space and limiting the growth rate of global routing state.
But at this point in the course, we just need to acknowledge that subnet masks can be anything between /0 to /32. More of this in Subnetting.
Reserved Addresses
Within the address spaces, but still not permitted to use:
- Loopback IP addresses are between 127.0.0.0 - 127.255.255.255
- Handled by the operating system, the most notable being 127.0.0.1
- Link-local Addresses are between 169.254.0.0 - 169.254.255.255
- If there is a failure in contacting a DHCP Server, the client chooses a random link-local address
Public IPv4 vs Private IPv4 addresses
RFC 1918 - Address Allocation for Private Internets
Dated February 1996;
"The Internet has grown beyond anyone's expectations. Sustained exponential growth continues to introduce new challenges. One challenge is a concern within the community that globally unique address space will be exhausted."
This meant that it was ideal to re-use addresses where direct connection to the Internet wasn't necessary. These addresses could be Network Address Translated - NATted (later on the course) to public addresses.
Private address spaces were declared as
- 10.0.0.0 - 10.255.255.255 (10.0.0.0 / 8)
- 172.16.0.0 - 172.31.255.255 (172.16.0.0 / 12)
- 192.168.0.0 - 192.168.255.255 (192.168.0.0 / 16)
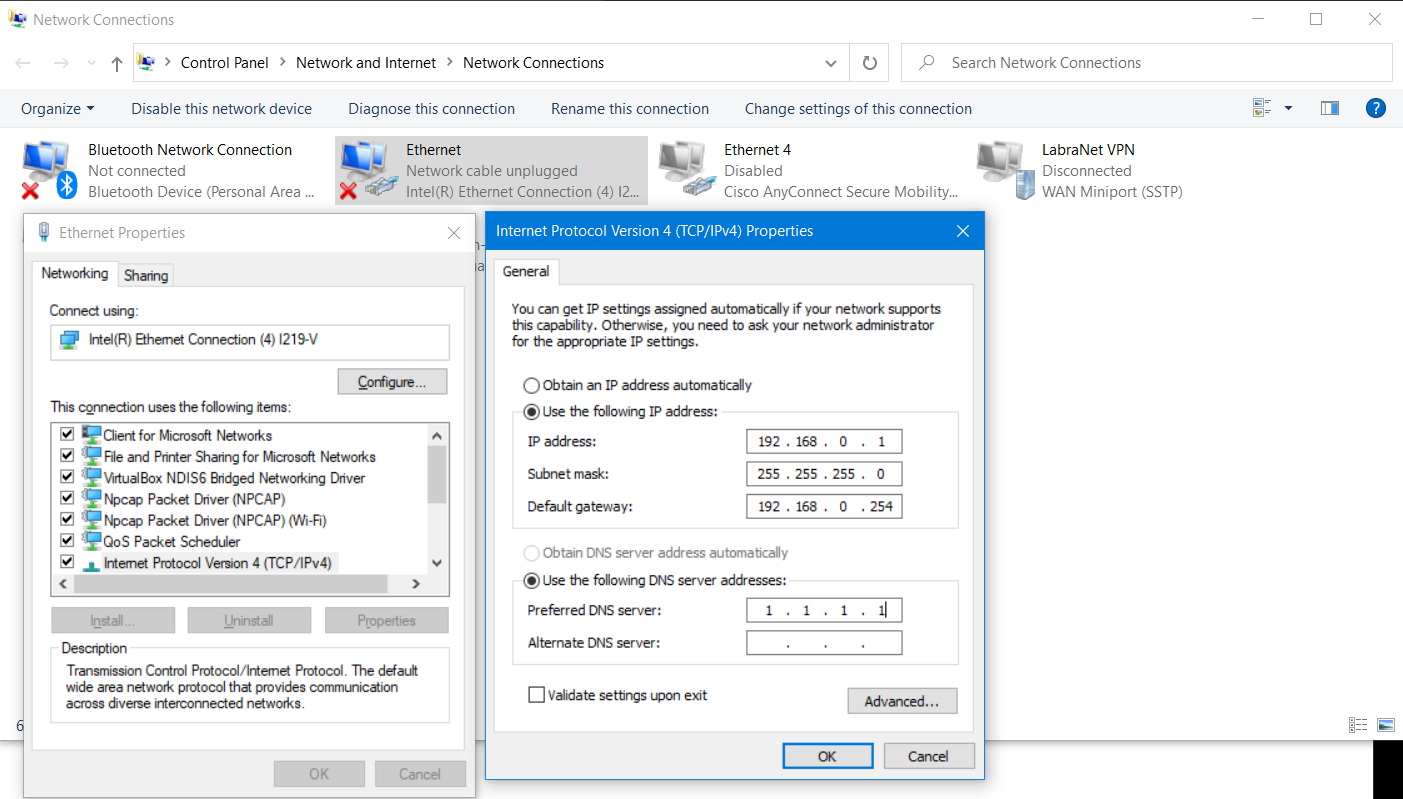
Addressing Windows 10
Here is an example of manual addressing of a Windows 10 machine.
Note that you have used to dynamic addressing, but you can only automate things once you understand how they are done manually.
DHCP - Dynamic Host Control Protocol is learned later on the course!
Windows knows this as the term Obtain an IP address automatically to activate DHCP client.
Given the figure, note the fields
- IP address: an IP address given to the device for use
- Subnet mask: the subnet size in DEC format, 255.255.255.0 would be /24 in
slash format - Default gateway: note that the term gateway lives on here rather than router, this is the gateway out of the subnet... similar to a door out of a classroom being the default gateway to access the world
And
- Preferred DNS server: devices need to translate domain names to IP addresses, DNS is discussed later on the course
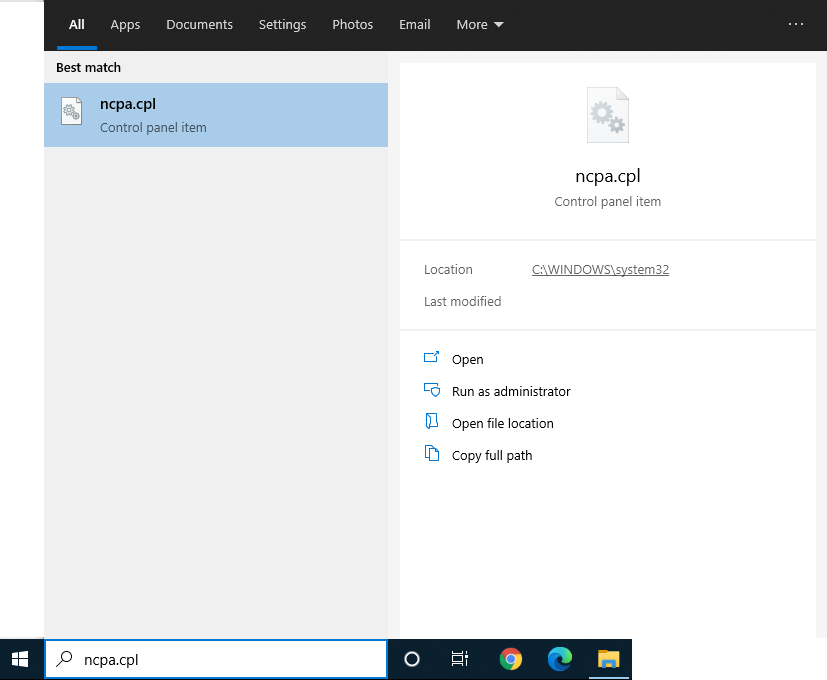
The settings can be found in Windows 10 by pressing the WIN button and typing ncpa.cpl
-
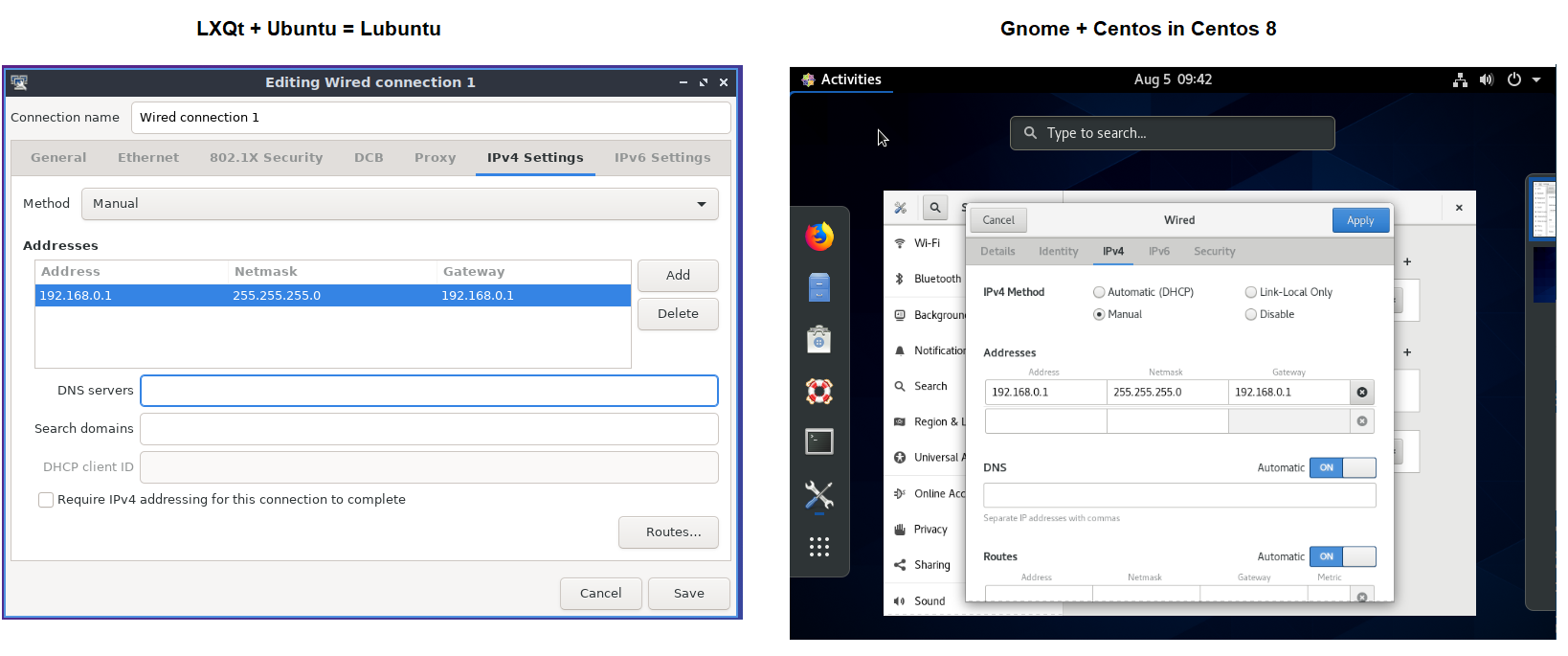
From the Network Connections, choose the Adapter you want to configure by right click + Properties
-
Select
Internet Protocol Version 4 (TCP/IPv4)and clickProperties
Linux world has same principles, but the graphical interface changes a little bit and are behind different windows/selection boxes
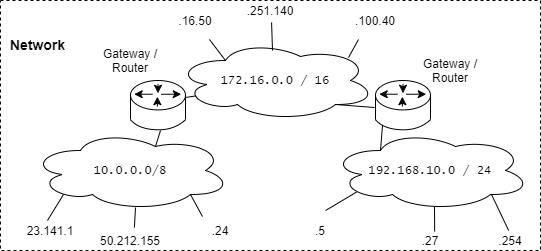
Routing
Lecture Video from this point forward
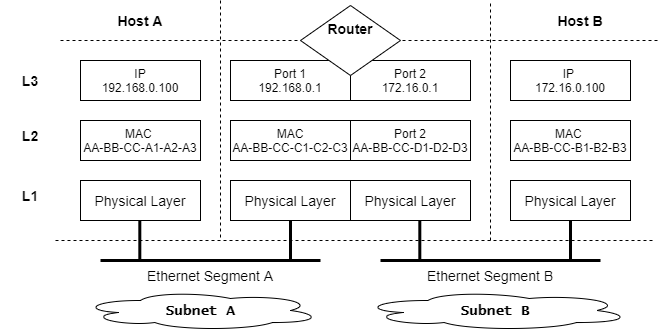
Between the subnets are gateways (or routers). They are represented in topology drawings with the logo:
They make the decision to forward traffic between subnets introduced earlier.
Routing at the simplest form is to look at the Destination Address of an IP packet and decide what interface it has to be sent out of.
Gateways / Routers
The earlier RFCs talked about gateways, but now-a-days they are called Routers.
Routers work on the OSI Layer 3 by forwarding packets.
What does a Router actually look like?
Routers found at home are usually (partly) managed by the ISP, but owned by the customer. They integrate a lot of functionalities in one box.
- OSI Model Layer 1: modem (4G/5G to WLAN to Cabled Ethernet),
- OSI Model Layer 2: switch
- OSI Model Layer 3: router
- ...
Routers in industrial use are typically more heftier e.g. Cisco ASR 1002-HX Router below
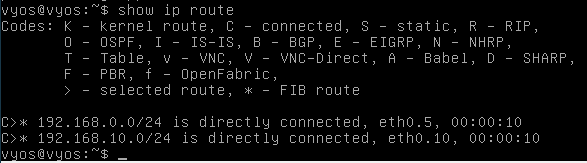
Routing Table
Given the topology above, Routing Table is a database that the router collects and maintains.
| Adapter | IP Network | Mask | Interface |
|---|---|---|---|
| 1 | 192.168.0.0 | / 24 | Ethernet 1 |
| 2 | 172.16.0.0 | / 16 | Ethernet 2 |
If the router receives a packet destined for 192.168.0.100, it can calculate the subnet it belongs to and send it out of the correct interface. By looking at the table above, it would be Ethernet 1.
Subnetting
Lecture Video from this point forward
The Math
Subnet Masks
The idea of subnet masks is to declare how many of the address bits are the network section (n) and how many are the host/device section (h). In the following example the mask is /24, so
- 24 pieces of n bits
- 8 bits of h bits
So if the address is 192.168.0.100 = 1100 0000 . 1010 1000 . 0000 0000 . 0110 0100
And the subnet mask is 255.255.255.0 = 1111 1111 . 1111 1111 . 1111 1111 . 0000 0000
If we count all the 1 bits of the subnet mask, we come to the total sum of 24. Thus 24 times 1 bits is represented by /24.
To help humans visualize this; now imagine all the 1 bits are represented by n bits (network bits) and all the 0 are h bits as follows,
nnnn nnnn . nnnn nnnn . nnnn nnnn . hhhh hhhh
What is the subnet?
Now you can use the n bits (or just the subnet mask directly in binary format) and place it next to the given address.
1100 0000 . 1010 1000 . 0000 0000 . 0110 0100 (typically the address goes first)
1111 1111 . 1111 1111 . 1111 1111 . 0000 0000 (then the subnet mask)
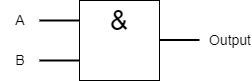
Now we look at the first bits of both of the rows.
1 = input A
1 = input B
Both are ran through and AND -gate.
Truth table of AND.
| Input A | Input B | Output |
|---|---|---|
| 0 | 0 | 0 |
| 0 | 1 | 0 |
| 1 | 0 | 0 |
| 1 | 1 | 1 |
Thus with the inputs above 1and 1, the output is 1.
When we go through all of the bits, we get the result of
1100 0000 . 1010 1000 . 0000 0000 . 0000 0000 = 192.168.0.0
Which is called the subnet address. Typically the size of the subnet is represented after the address, e.g. 192.168.0.0/24.
How many hosts can fit into the subnet?
Now you can use the h bits to get the "size of the subnet". It answers to the question; "how many hosts can the subnet fit?"
We had 8 h bits. We cycle through all of them.
| binary | decimal | purpose |
|---|---|---|
| 0000 0000 | 0 | Subnet address |
| 0000 0001 | 1 | 1st host address |
| 0000 0010 | 2 | 2nd host address |
| 0000 0011 | 3 | 3rd host address |
| 0000 0100 | 4 | 4th host address |
| .... .... | . | ................ |
| 1111 1100 | 252 | 252th host address |
| 1111 1101 | 253 | 253th host address |
| 1111 1110 | 254 | 254th host address |
| 1111 1111 | 255 | Broadcast Address |
Thus if we take out the Subnet Address and Broadcast address we get 254 usable addresses.
Otherway to calculate the "size of the subnet" is to have formula: 2^h - 2
2^8 - 2 = 254, where -2 comes from the subnet address and broadcast address being unavailable for host use.
Supernetting vs Subnetting
Lecture Video from this point forward
This is called Variable Length Subnet Mask - VLSM
Supernetting is to increase the "size of the subnet". The goal is to increase the amount of hosts that fit into the subnet.
/23 -> 2^9 - 2 = 510 hosts
/22 -> 2^10 - 2 = 1022 hosts
/21 -> 2^11 - 2 = 2046 hosts
Note worthy is that this takes away the bits from the subnet mask (the n bits decrease and the h bits increase). E.g.
/22 =
nnnn nnnn . nnnn nnnn . nnnn nnhh . hhhh hhhh =
1111 1111 . 1111 1111 . 1111 1100 . 0000 0000 =
255.255.252.0
As the host bits increase to 10, we get a supernet of 2^10 - 2 = 1022
Subnetting is to decrease the "size of the subnet". The goal is to decrease the amount of hosts that fit into the subnet.
/25 -> 2^7 - 2 = 126 hosts
/26 -> 2^6 - 2 = 62 hosts
/27 -> 2^5 - 2 = 30 hosts
Noteworthy is that this increases the bits of the subnet mask (the n bits increase and the h bits decrease).
/26 =
nnnn nnnn . nnnn nnnn . nnnn nnnn . nnhh hhhh =
1111 1111 . 1111 1111 . 1111 1111 . 1100 0000 =
255.255.255.192
As the host bits decrease to 6, we get a subnet of 2^6 - 2 = 62
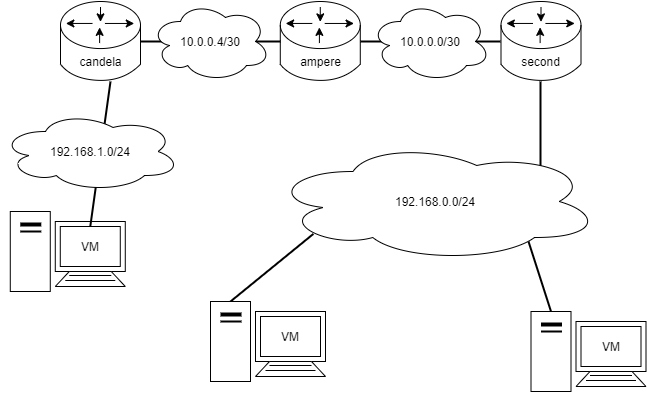
Design & Documentation
In IPv4 the design is to use as little IPv4 addresses as possible, but still room for possible growth.
Typically this means:
- links between devices are subnetted with
/30 - local area networks with
/24(because of tradition of class C subnets).- Smaller are suggested if plausible to conserve public IP address space
Still other varying subnets might occur, and thus calculation is a basic knowhow of an engineer in IT.
With this design, a typical network would look like:
Address Resolution Protocol - ARP
Lecture Video from this point forward
ARP is the glue between OSI Model Layer 3 and Layer 2. This means that there are multiple occasions when an MAC Address is needed for an IP address and vice versa.
Everytime a network device needs to know this information (e.g. to forward traffic). ARP comes into play.
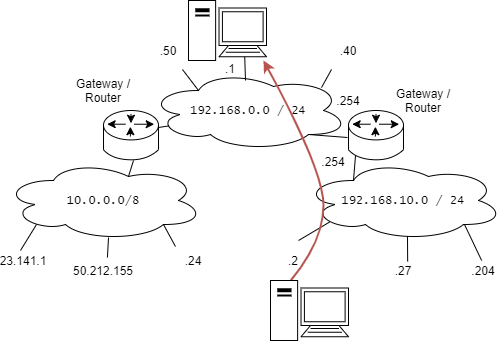
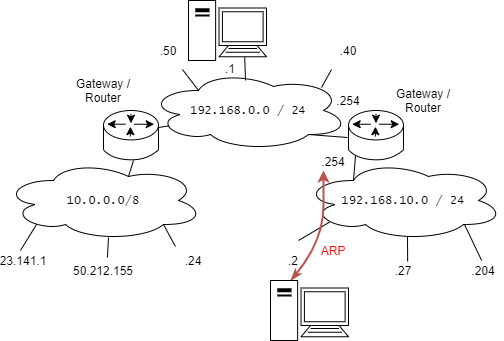
The following examples happen when 192.168.10.2 needs to send traffic to 192.168.0.1 presented in the following diagram.
When devices are given IP addresses, they only know their own IP and MAC address. This can be seen below when checking the IP address of lubuntu.
lubuntu@lubuntu-VirtualBox:~$ ip addr
1: eth0: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc pfifo_fast state UP group default qlen 1000
link/ether 08:00:27:0e:55:17 brd ff:ff:ff:ff:ff:ff
inet 192.168.10.2/24 brd 192.168.10.255 scope global eth0
valid_lft forever preferred_lft forever
inet6 fe80::a00:27ff:fe0e:5517/64 scope link
valid_lft forever preferred_lft forever
Ethernet adapter Ethernet:
Connection-specific DNS Suffix . :
Description . . . . . . . . . . . : Realtek PCIe GBE Family Controller
Physical Address. . . . . . . . . : BC-AE-C5-24-74-1D
DHCP Enabled. . . . . . . . . . . : Yes
IPv4 Address. . . . . . . . . . . : 192.168.0.21(Preferred)
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Lease Obtained. . . . . . . . . . : Wednesday 3. February 2021 8.10.21
Lease Expires . . . . . . . . . . : Wednesday 3. February 2021 13.10.21
Default Gateway . . . . . . . . . : 192.168.0.1
DNS Servers . . . . . . . . . . . : 8.8.8.8
The machine needs to contact its default gateway (or the router connecting the subnet) to forward traffic out of its own subnet. So ARP works between these devices.
When the device is addressed, it is given a gateway address. This can be checked by looking at the routing table of the computer.
lubuntu@lubuntu-VirtualBox:~$ route -v
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
default 192.168.10.254 0.0.0.0 UG 0 0 0 eth0
192.168.10.0 * 255.255.255.0 U 1 0 0 eth0
Note here that the gateway term lives on. Even though people are talking about routers!
C:\Users\sahka>route print
~~~ tulostetta poistettu ~~~
IPv4 Route Table
===========================================================================
Active Routes:
Network Destination Netmask Gateway Interface Metric
0.0.0.0 0.0.0.0 192.168.10.254 192.168.10.2 25
192.168.10.0 255.255.255.0 On-link 192.168.10.2 281
192.168.10.2 255.255.255.255 On-link 192.168.10.2 281
192.168.10.255 255.255.255.255 On-link 192.168.10.2 281
===========================================================================
Persistent Routes:
None
Note here that the gateway term lives on. Even though people are talking about routers!
The information on the computer now is, and this is called the ARP table:
| IP address | MAC address |
|---|---|
| 192.168.10.2 | 08:00:27:0e:55:17 |
| 192.168.10.254 | ? |
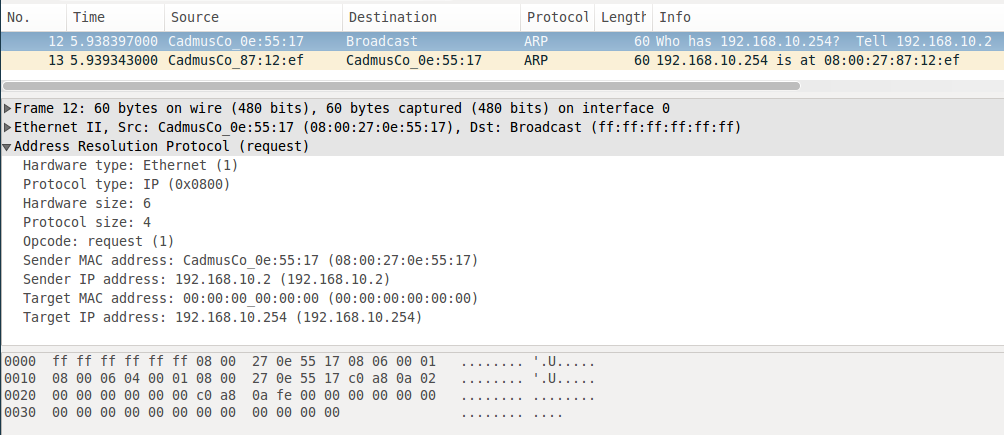
Now the computer needs to send an ARP message to the whole subnet (a broadcast) to find out what is the MAC address of 192.168.10.254. This is represented in the figure below.
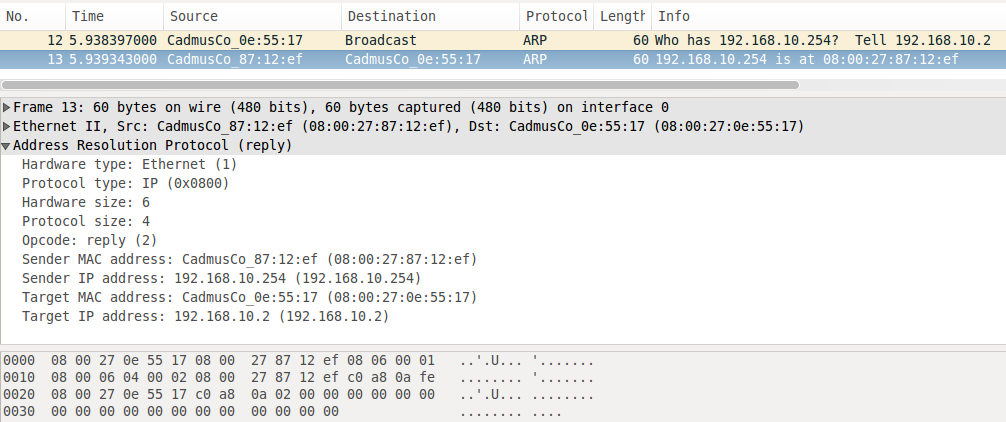
The answer can be seen below.
When this message transaction is done. The computer now knows the ARP table (checked by the command arp -a)
lubuntu@lubuntu-VirtualBox:~$ arp -a
? (192.168.10.254) at 08:00:27:87:12:ef [ether] on eth0
C:\Users\sahka>arp -a
Interface: 192.168.0.201 --- 0xe
Internet Address Physical Address Type
192.168.10.254 08-00-27-87-12-ef dynamic
Thus the ARP table is now fulfilled and traffic can continue.
| IP address | MAC address |
|---|---|
| 192.168.10.2 | 08:00:27:0e:55:17 |
| 192.168.10.254 | 08:00:27:87:12:ef |
Continue to the Exercises
Self-reflect the material with a small quiz?
![]() Data Networks Quiz - M03 IPv4 Addresses, Subnetting and ARP
Data Networks Quiz - M03 IPv4 Addresses, Subnetting and ARP
Back to the Schedule?
License
This course and its materials are written by Karo Saharinen and licenced by Attribution-NonCommercial-NoDerivatives 4.0 International (CC BY-NC-ND 4.0) license.